[ad_1]
Linux has yet one more high-severity vulnerability that makes it straightforward for untrusted customers to execute code able to finishing up a bunch of malicious actions together with putting in backdoors, creating unauthorized consumer accounts, and modifying scripts or binaries utilized by privileged companies or apps.
Soiled Pipe, because the vulnerability has been named, is among the many most critical Linux threats to be disclosed since 2016, the 12 months one other high-severity and easy-to-exploit Linux flaw (named Soiled Cow) got here to gentle because it was getting used to hack a researcher’s server. Researchers in 2016 demonstrated the best way to exploit Soiled Cow to root any Android telephone whatever the the cellular OS model. Eleven months later, researchers unearthed 1,200 Android apps in third-party markets that maliciously exploited the flaw to just do that.
When No one turns into all highly effective
The identify Soiled Pipe is supposed to each sign similarities to Soiled Cow and supply clues in regards to the new vulnerability’s origins. “Pipe” refers to a pipeline, a Linux mechanism for one OS course of to ship knowledge to a different course of. In essence, a pipeline is 2 or extra processes which might be chained collectively in order that the output textual content of 1 course of (stdout) is handed instantly as enter (stdin) to the following one.
Tracked as CVE-2022-0847, the vulnerability got here to gentle when a researcher for web site builder CM4all was troubleshooting a sequence of corrupted information that stored showing on a buyer’s Linux machine. After months of study, the researcher lastly discovered that the shopper’s corrupted information have been the results of a bug within the Linux kernel.
The researcher—Max Kellermann of CM4all guardian firm Ionos—finally discovered the best way to weaponize the vulnerability to permit anybody with an account—together with least privileged “no person” accounts—so as to add an SSH key to the foundation consumer’s account. With that, the untrusted consumer might remotely entry the server with an SSH window that has full root privileges.
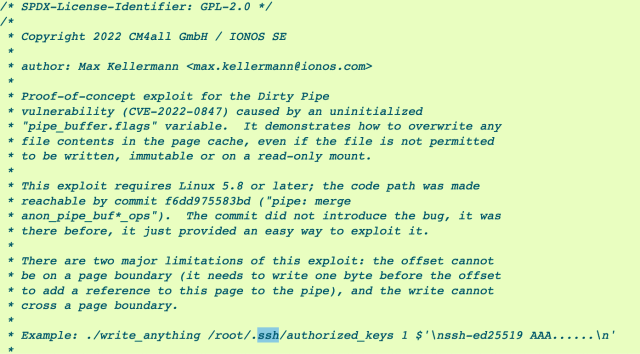
Different researchers rapidly confirmed that the unauthorized creation of an SSH key was solely one in all many malicious actions an attacker can take when exploiting the vulnerability. This program, as an example, hijacks an SUID binary to create a root shell, whereas this one permits untrusted customers to overwrite knowledge in read-only information:
Different malicious actions enabled by Soiled Pipe embrace making a cron job that runs as a backdoor, including a brand new consumer account to /and many others/passwd + /and many others/shadow (giving the brand new account root privileges), or modifying a script or binary utilized by a privileged service.
“It is about as extreme because it will get for an area kernel vulnerability,” Brad Spengler, president of Open Supply Safety, wrote in an e mail. “Identical to Soiled Cow, there’s primarily no method to mitigate it, and it entails core Linux kernel performance.”
The vulnerability first appeared in Linux kernel model 5.8, which was launched in August 2020. The vulnerability persevered till final month, when it was mounted with the discharge of variations 5.16.11, 5.15.25 and 5.10.102. Just about all distributions of Linux are affected.
Throwing a wrench in Android
Soiled Pipe additionally afflicts any launch of Android that is based mostly on one of many susceptible Linux kernel variations. Since Android is so fragmented, affected system fashions cannot be tracked in a uniform foundation. The newest model of Android for the Pixel 6 and the Samsung Galaxy S22, as an example, run 5.10.43, which means they’re susceptible. A Pixel 4 on Android 12, in the meantime, runs 4.14, which is unaffected. Android customers can test which kernel model their system makes use of by going to Settings > About telephone > Android model.
“The Soiled Pipe vulnerability is extraordinarily critical in that it permits an attacker to overwrite—briefly or completely—information on the system they shouldn’t be in a position to change,” Christoph Hebeisen, head of safety analysis at cellular safety supplier Lookout, wrote in an e mail. “Attackers can use this to alter the conduct of privileged processes, successfully gaining the potential to execute arbitrary code with in depth system privileges.”
The Lookout researcher stated the vulnerability will be exploited on Android handsets by way of a malicious app that elevates its privileges, which by default are alleged to be restricted. One other avenue of assault, he stated, is to make use of a special exploit to achieve restricted code execution (for instance, with the system rights of a reliable app that is hacked) and mix it with Soiled Pipe so the code good points unfettered root.
Whereas Kellermann stated that Google merged his bug repair with the Android kernel in February, there aren’t any indications Android variations based mostly on a susceptible launch of the Linux kernel are mounted. Customers ought to assume that any system operating a model of Android based mostly on a susceptible model of the Linux kernel is vulnerable to Soiled Pipe. Google representatives did not reply to an e mail searching for remark.
[ad_2]
Source link

